We’ve seen a shift in bug bounty programs and offensive security capabilities with the rapidly changing AI landscape. Recently, the Internet Bug Bounty Program has paused bounties and Anthropic announced the security capabilities of their newest model, Mythos. As a downstream impact of the IBB change, Node.js announced a pause of their bug bounty program.
AI has and will continue changing cybersecurity. One area that is fundamentally changed is white hat hacking (bug bounty and vulnerability disclosure programs) where AI is used for offensive cybersecurity. In this post, we'll look at a data-driven approach at recently changed bug bounty programs including curl.
We've seen AI overwhelm bug bounty and security programs and expect this to continue as AI Models improve and adoption of AI continues.
- In April 2026, one program changed their SLA for response from 2 to 5 days and their triange SLA from 2 to 10 days. That's a 5x increase in time for triage.
- With curl, we've seen average monthly submissions go from 2.92 in 2024 to 16 in 2026 even after pausing financial rewards. That's over a 5.4x increase in report volume.
- In 2025, HackerOne reported that 73% of programs saw a drop in valid submissions.
- HackerOne even offers Report Assistant pitched to "write reports faster with our Hai-powered agent."
HackerOne Background
Let's first look at an overview of how HackerOne works. HackerOne is a platform used by many enterprises to host a bug bounty or vulnerability disclosure program. Curl's program is hosted on HackerOne and all findings are supposed to be submitted via HackerOne.
HackerOne has the following closed finding states:
- N/A (Not Applicable)
- Informative
- Resolved (Low, Medium, High, Critical)
- Spam
- Duplicate
We can simplify to the following categories:
- Resolved: A good quality and valid security finding (generally fixed by disclosure).
- Informative: a good quality find, but not impactful enough to be a security find.
- N/A and Spam: "Slop" reports and considered invalid.
curl's Bug Bounty Program and History
Curl's program is a good early warning system of industry trends due to the following:
- Curl is open source, which means hackers can run tooling on source code. This is not the case for closed source programs, which require different reconnaissance, enumeration, and hacking strategies.
- Curl is unique as their policy on HackerOne is to disclose all security reports for transparency. This gives us the ability to dive into their reporting and history.
We analyzed all 413 reports and pulled data on April 13th, 2026. Below is our analysis and trends we've observed from curl's program on HackerOne.
At the end of January 2026, curl officially ended their Bug Bounty Program hosted on HackerOne. In stats posted by Daniel Stenberg (cURL founder, CEO, lead developer), cURL has paid over $100,000 USD for 87 confirmed vulnerabilities at the time of his blog post. Previously in mid 2025, Daniel blogged about how slop (both human and AI) was hurting curl.
However, in a post on Linkedin on April 6th 2026, Daniel posted the following “Over the last few months, we have stopped getting AI slop security reports” and “Instead we get an ever-increasing amount of really good security reports, almost all done with the help of AI.”
Let's first look at monthly submissions over time. It's important to note the following dates:
- January 31st, 2026: End of Bug Bounty Program (Financial Rewards)
We use a baseline of average monthly submissions prior to 2025 (2.36) to show the recent increase in submissions.
Despite the bug bounty program ending, we see a continued increase in findings submitted per month. We surmise this is due to AI-assisted bug hunting which reduces the effort and expertise needed to submit and write findings. This is even before general access to Claude Mythos.
Let's now look at spam and N/A reports. We see the trend largely mirrors the increase in reports, which is understandable. As quantity of reports increase, we expect to see an increase in invalid (spam and N/A) reports. Again, we use a baseline of average submissions prior to 2025 (0.66) to show the recent increase in invalid reports.
But what about "good" reports. Let's look at only resolved reports - reports that are valid and rated as either critical, high, medium, or low severity. From this chart, we do not see any significant trends with resolved reports.
For our next analysis, we combined informative reports. Informative reports do not impact submitter's statistics on HackerOne and are typically regarded by programs as good quality reports, but may not meet the criticality rating to be considered a true security issue. We do see a slight increase in valid findings submissions per month even after payments were removed from the program.
Transitioning from a Paid Bug Bounty Program to a Non-Paid Vulnerability Disclosure Program
On February 1st, 2026, cURL paused financial rewards as a response to the increasing number of AI Slop reports. We don't find this as a good long term strategy as financial rewards are a strong incentive for researchers to engage with programs and look for security vulnerabilities.
However, we do see pausing financial rewards as a way to remove "slop" reports as it de-incentivizes submissions focused solely on financial reward.
Let's look at the data from cURL. We will compare numbers between 2 time periods: numbers from the year prior to cURL pausing financial rewards and numbers onward from cURL pausing financial rewards.
As the data indicates, the percentage of slop reports (N/A and Spam) decreased significantly while the number of valid and quality reports increased (both Resolved and Informative).
Let's take a look at quantity of submissions and normalize by looking at average submissions by month. We look at 3 distinct time periods:
- 2024
- 2025 (Uptick in AI-related usage)
- February and March 2026 (first full months of VDP)
We can see that the average number of submissions continue to increase over time while the average number of "slop" reports increased in 2025, and then dropped after curl stopped paying for reports.
Observations
Report submission has gone up
With curl (and also from other programs that we've been involved in), we've seen report numbers go up. We believe this can be directly attributed to researchers either using AI-assistance or completely using AI to submit reports. Using curl as an example, there's been a 5.4x increase in reports despite removing financial rewards.
We expect to see report submission increase and also expect to see programs try to keep up either by de-incentivizing low quality submissions or adopting AI in processes for triage.
Impact on Programs
We can simplify the process of bug bounty hunting into 3 phases:
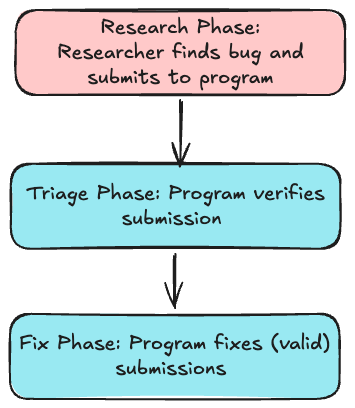
With AI-assistance, the research phase's cost from a resource, knowledge, and time perspective has been shortened. Writing reports and also the ability to write invalid reports that look valid are now much easier. This puts more strain on the program in both the triage phase and fix phase. For open source tooling, time is a finite resource and triaging and fixing can take a considerable amount of time.
Part of the difficulty with handling reports is triage. Even if a report looks to be AI-generated or to be potentially low quality, the report still needs to be triaged in the case that it's a valid security concern.
Triage Overload
With report cost going down, more researchers are able to submit reports to programs. With AI assistance, low-quality reports can look more believable with code snippets, writing and thus take more time to triage. We've seen one program shift their SLAs earlier this month from 2 days to 10 days for triage. That's a 5x increase in triage time. We expect this to continue to be a bottleneck for now, until AI can truly be used to assist with triage without removing true vulnerabilities.
Conclusion
AI has completely changed offensive security. We're seeing significant changes in bug bounty and vulnerability disclosures including a 5x increase in triage time and a 5x increase in report volume. This puts strain on
We expect to see security teams try to keep up with the adoption of AI for offensive security. In the short term, we expect to see more private programs to reduce access to submitting reports, more transition to VDPs and removal of financial incentives to remove low-effort reports, and even paused programs as teams become overwhelmed. In the longer term, we expect to see continued adoption of AI in the triage and remediation pipelines.
References
- https://hackerone.com/curl
- https://github.com/curl/curl/pull/20312
- https://daniel.haxx.se/blog/2026/01/26/the-end-of-the-curl-bug-bounty/
- https://daniel.haxx.se/blog/2025/07/14/death-by-a-thousand-slops/
- https://www.linkedin.com/posts/danielstenberg_hackerone-share-7446667043380076545-RX9b/
- https://red.anthropic.com/2026/mythos-preview/
- https://hackerone.com/ibb
- https://nodejs.org/fr/blog/announcements/discontinuing-security-bug-bounties